BlueCat DNS Edge Just Got More Powerful
The latest release of DNS Edge is now live and includes a number of new features like multi-namespace support for better routing, enhanced volumetric tunneling detection, dashboard improvements, and other foundational enhancements.

The latest release of DNS Edge is now live and includes a number of new features like multi-namespace support for better routing, enhanced volumetric tunneling detection, dashboard improvements, and other foundational enhancements.
Multi-Namespace Support
Since DNS Edge is implemented in the recursive layer, it has the unique advantage of logging and analyzing all queries from clients on the network, but the way it is implemented can also benefit and optimize your environment. With this new release of DNS Edge, users will have more flexibility in configuring their DNS resolution path. They can easily route queries targeting select domains to a specific group of forwarders using Match & Exception domain lists. Not only can they name up to 3 Namespaces as default, but they can set different Namespaces at the Site level, with each Namespace being able to handle hundreds of domains.
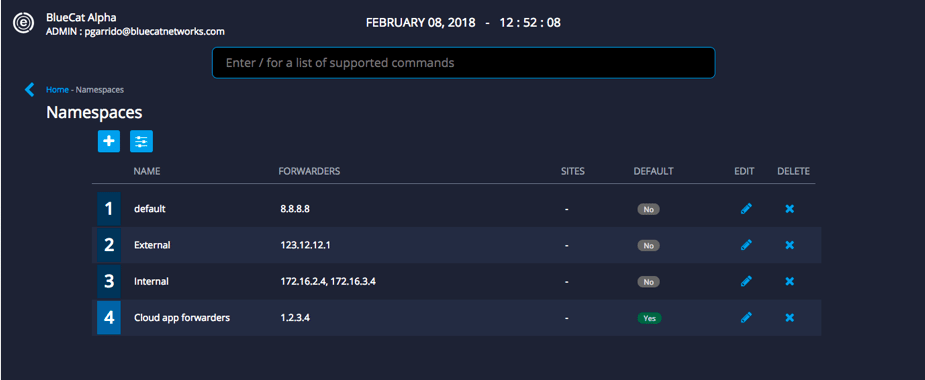
Why is this important? Here are a few examples of how you can leverage Multi-Namespace:
1. Avoid unnecessary sets of records for both internal and external requests.
For example, if there’s an HR web application that both internal employees and external contractors need to access to, there’s no need to maintain identical records for the application on both zones.
Practically speaking, the first Namespace will be an internal list of forwarders; the second will be an external list of forwarders, including the HR web application. When an internal request for the HR web application is made, it will go to the internal Namespace first (assuming it’s prioritized first in the default list); the forwarder will resolve an NXDOMAIN and the query will travel to the second Namespace (in this case, the external forwarders) where it will be successfully resolved. Administrators can maintain a single record for the same sources used by more than one zone simplifies management for Administrators, avoiding common issues of maintaining duplicate records.
2. Lighten the load on internal servers for traffic intended for trusted cloud apps.
Trusted cloud apps that are used regularly on the network like Office365.com can place an unnecessary load on internal servers. An Exception list can be configured for the first Namespace to forward select cloud applications like Office365.com to forward traffic directly to the Authoritative server. This helps in offloading traffic from their internal servers from needing to answer queries for these cloud applications.
This new feature opens up many possibilities and we expect DNS Edge customers will discover many additional use cases that improve overall query performance.
Threat Detection Analytics Updates
DNS tunneling, the technique of performing data exfiltration by encoding data of other programs or protocols in DNS queries and responses, is a major concern for all security professionals. DNS Edge analyzes all queries and flags for methods such as tunneling and domain generation algorithms, but we also continue to optimize our analytics engine.
In the latest updates to DNS Edge, we’ve refined our data exfiltration detection via volumetric tunneling to minimize false-positives. A newly developed System Tunneling List will compile compromised domains suspected of tunneling, and with Tunneling “block” policy configured, these domains will be prevented from resolving. We’ve also updated our volumetric detection capabilities to be based on regular polling of the last hour’s worth of data and looking for common domains that exhibit the signs of the type of tunneling we look for.
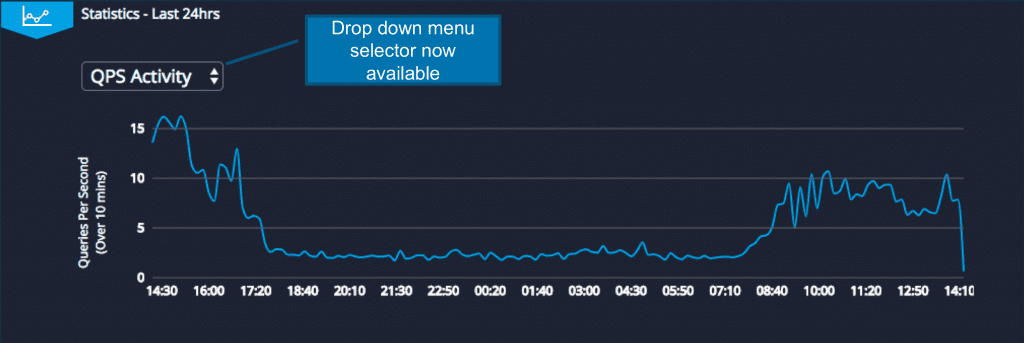
DNS Activity Dashboard and Admin Enhancements
The statistics pane now includes a drop-down menu that allows clients to choose between viewing a line-graph displaying Queries Per Second (QPS) or previously displayed Policy Activity.
Also, Admins can now create Analyst user roles which will enable them to view the DNS Activity and Threat Activity tables without having access to any other screens.
With these new updates to DNS Edge, you’ll not only be better able to detect and analyze potential malicious activity, but you’ll be able to optimize your DNS infrastructure.