Blog
Check out the latest in network management, cybersecurity, and DDI.

Get fast, resilient, and flexible DDI management with Integrity 9.6
With Integrity 9.6, network admins can get support for new DNS record types, architect and configure multi-primary DNS, and automate IP assignments.
Deepen your security insight with Infrastructure Assurance 8.3
BlueCat Infrastructure Assurance 8.3, with an enhanced analytics dashboard, including interactive widgets and top 10 alerts, is now available.

Security, automation, cloud integration keys to DDI solution success
Only 40% of enterprises believe they are fully successful with their DDI solution. Learn how to find greater success with new research from EMA and BlueCat.

Our commitment to Micetro customers and product investment
From CEO Stephen Devito, a word on BlueCat’s ongoing commitment to supporting Micetro customers and Micetro’s evolution as a network management tool.

Seven reasons to rethink firewall monitoring and boost automation
With BlueCat Infrastructure Assurance, you can better protect your network with automated alerts and suggested remedies for hidden issues in your firewalls.

Five ways to avert issues with BlueCat Infrastructure Assurance
By flagging and notifying you of hidden issues before they cause damage, you can go from reactive to proactive in your Integrity DDI environment.

Enhancing DDI automation and security with Men&Mice and Indeni
Following its recent acquisitions, BlueCat now offers DDI orchestration with Micetro and proactive monitoring of DDI devices with Infrastructure Assurance.

Enhance DNS control with BlueCat Edge SPv4
With a multi-service architecture, BlueCat Edge SPv4 now supports simultaneous add-on modules for security, networking, cloud, and branch offices.

Cisco Live 2023: Introducing Zero Trust DNS
Unveiled at Cisco Live, Zero Trust DNS from BlueCat offers continuous verification, least-privilege access, and context and response to secure networks.

BlueCat is now a Cisco SolutionsPlus partner
BlueCat’s alliance with Cisco delivers leading DDI solutions to Cisco customers as part of Cisco’s integrated networking and security environments.

No. 1 driver of DDI investment: automation
EMA research found that automation is the top reason small and medium international enterprises invest in DDI solutions. What drives your enterprise?

Manifest V3 doubts? Try a DNS-based solution
Learn how Google Manifest V3 changes may impact anti-tracking and ad blockers and how a DNS solution might be a better option for your enterprise network.

Inside our Serbia customer care center launch
Learn why Serbia is an ideal fit for expansion and go behind the scenes of the opening of our new Customer Care and Integration Development Center.

Our process for a successful BlueCat migration
Explore the details of our proven methodology and the specific processes we use to ensure successful migrations to BlueCat’s Adaptive DNS solution.

Four steps to succeed with your DDI solution
New EMA research on implementing DDI solutions highlights four ways to ensure success, starting with dumping DIY approaches. Are you ready to begin?

Cloud, automation, security drive DDI pursuit
EMA research found that cloud, automation, and security are the three primary drivers behind investing time or money in DDI technology. What drives you?

Two-thirds of enterprises employ full-stack DDI
EMA research found three distinct stages of DDI maturity, with 65% of enterprises realizing the value of a full-stack DDI solution. Is yours one of them?

Keep system issues at bay with health checks
Two levels of BlueCat support offer health checks to analyze customers’ system data for potential problems and fix them before they take networks down.
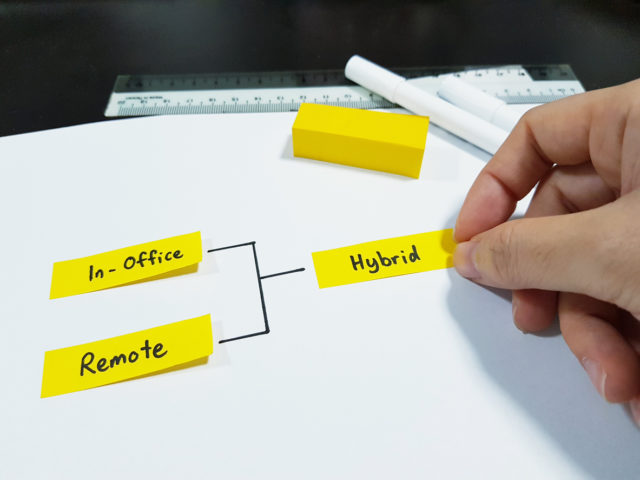
Security, IT tools, and right policies key for hybrid work
Cisco Live 2022 emphasized the hybrid work future, but security, the right tools and skills for network teams, and policy alignment to technology are key.

How cloud platforms build the business of experience
Accenture Managing Director Maya Agaskar discusses how a platform-based approach and the business of experience can aid digital transformation journeys.

Shift to cloud is shifting IT skill and training needs, too
CompTIA Chief Technology Evangelist James Stanger discusses why IT professionals need automation skills and how to take control of your own learning.

For network automation decisions, metrics are key
Uber engineer Ryan Patterson shares how data drives network automation projects, which must also be scalable, save costs, and meet user needs.

Key to DevOps success: avoid lift and shift to cloud
GM Financial’s DevOps VP Matt McComas offers key lessons on taking a systemic approach, breaking process roadblocks, and measuring automation success.

The war in Ukraine: A message from CEO Stephen Devito
BlueCat has discontinued the export of our products and services, as well as support, for all customers owned and operated in Russia or Belarus.
Get in touch
We’re the DDI provider you’ve been looking for.
Drop us a line and let’s talk.